Encryption types: WEP, WPA and WPA2
It is a well-known rule of Wi-Fi networking is that you should never leave your network unprotected. When Wi-fi networks were introduced it was not uncommon for individuals or even companies for that matter to leave their networks unprotected. This would mean it would allow them internet access, as well as access to their networks. If someone can gain access to your network them this means your data is at risk. Therefore it is Important to encrypt your network, and this occurs through security protocols called WEP, WPA and WPA2.
WEP security algorithm
The WEP security algorithm (Wired Equivalent Private) is a security protocol, specified in the IEEE Wireless Fidelity (Wi-Fi) standard, 802.11b protocol, was introduced in 1999 and designed to provide a local area network (WLAN) on Same level of security and privacy as a LAN wired network.
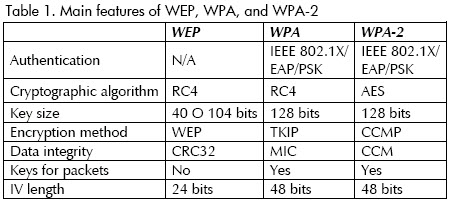
Wireless networks with WEP encryption are less secure than LANs that WLAN radio waves encrypt the data flow using the key. This key is stored for the network adapters of the devices and is used to decrypt and encrypt the packets sent or received. With wireless audit tools like Aircrack-ng it is possible to hack a red in minutes. That is why in 2004 it became the WPA encryption protocol and later WPA2 to replace the vulnerabilities of the WEP protocol.

Wi-Fi Protected Access
WPA (Wi-Fi Protected Access) was used as a security enhancement using TKIP (Temporal Key Integrity Protocol), but like WEP it was still insecure and vulnerable. In the protocol based on 802.11i wireless security standards, WPA2 was introduced, which was a modern WPA using a previously shared key (PSK) and the most advanced AES algorithm. The disadvantage offered by WPA2 was the high processing consumption for the decryption of information and the user gets greater protection.










Publicar comentario